Here is a scenario that will send chills down the spine of any UX researcher: Imagine you are in the field performing in-home interviews that involve new prototype designs for your company. While popping-in for a coffee between sessions, your laptop – which contains your notes and personal information about the participants – and a GoPro full of videos are stolen from the car.
It’s a worst-case scenario but is completely realistic.
Your participants are now at risk for identity theft, leakage of private information. Your company is at risk of losing valuable IP, credibility with customers and investors, and has opened itself to litigation from participants.
It’s a big mess that is completely avoidable by applying processes, policy and protection for the data that is gathered and stored during the course of conducting UX research.
Mature product teams are taking the privacy of user data much more seriously because of infamous data breaches such as Yahoo, Equifax and LifeLabs. An ethical user research approach demands user researchers also scrupulously protect the privacy of participants.
This means adopting practices for handling the private data of participants in ways that promote the security of their personal data.
We work with a significant amount of private data in every study we conduct. Our clients, which include large global tech and big government, trust us to protect private data.
This article outlines how we have aligned our research ops practices to promote a culture of data protection, upholding the privacy of our research participants and adhering to privacy frameworks to ensure we do not put personal data at risk, like the scenario mentioned above.
We began by applying GDPR (EU) and PIPEDA (Canada) principles to how we gather and store personally identifiable information (PII) across the user research lifecycle.
There are four critical principles that guide adherence to GDPR guidelines.
- Gather informed consent for any and all data processing.
- Only collect and store the information you need when you need it.
- Ensure all user data is being stored and processed securely (including by 3rd party tools).
- Give users control over their data.
So practically speaking, how do we adhere to these principles within a UX research project? We looked across a typical user research project lifecycle to identify where we collect data, how we use it, and how these principles should be applied.

Kick-off
- During kick-off we document the types of data we will be gathering from participants. Names, email addresses, physical addresses, demographic data are all typical types of data we collect.
Planning and recruitment
- The principal researcher creates a Project Privacy Statement document that informs participants about what data will be collected and how it will be used and processed during the study.
- Recruitment can happen either directly by our team or by a 3rd party recruiter. In either situation, we apply the following guidance:
- Participants will have informed consent and will be aware of the types of data that will be obtained during the research. We do this by providing them with a project privacy statement.
- Personally identifiable information (PII) must be secured both in transit and at rest. That means if an email is used to transmit data, it must be encrypted and password protected. Our laptops are encrypted to ensure PII is safely stored on local drives.
- Emails that contain participant sheets and contact information must be permanently deleted as soon as they have been downloaded to our laptops.
- We store XLS sheets in Dropbox for the duration of the project. Other secure services such as Google Sheets or Drive are also acceptable ways to share data amongst stakeholders – just remember to keep track of the disparate places you are storing data.
- We use survey tools such as Survey Monkey and Qualtrics for recruitment. Once the recruitment effort is completed, we permanently delete the data from these service providers. It’s important not to leave PII on 3rd party services; deleting the data minimizes the risk that 3rd party providers bring.
- Scheduling happens using Outlook and it contains participants' emails and contact details. We permanently delete calendar entries once interviews are completed.
- Participants are provided with the contact information to our Data Protection Officer. This is the person within the organization who is the point of contact about their personal data. They have the right to request their data be destroyed at any time during a project, so it is critical they have a point of contact who can assist them with this request.
Conducting research
There’s no avoiding the fact that vast amounts of PII are generated during the collection of qualitative data. Meeting with participants can happen in a lab, in their home, or online. In each of these spaces, we are asking for thoughts and opinions, recording audio and video, capturing observational notes. We follow a few simple guidelines at this step to ensure we are protecting data:
- Video cards are wiped and securely reformatted once the video is downloaded, which occurs daily. Video cards are password protected.
- All audio/video is stored in Dropbox, not on local machines. Should a local machine be required for editing or transferring video, it must be permanently shredded using specialized software once these tasks are completed.
- Participants are referred to by a participant number in observational notes.
- Paper notes are digitized and stored in Dropbox and shredded immediately.
Analyzing and reporting
- Participant data is anonymized for reports. Although their likeness is used in video highlights, any PII is redacted.
Closing the project
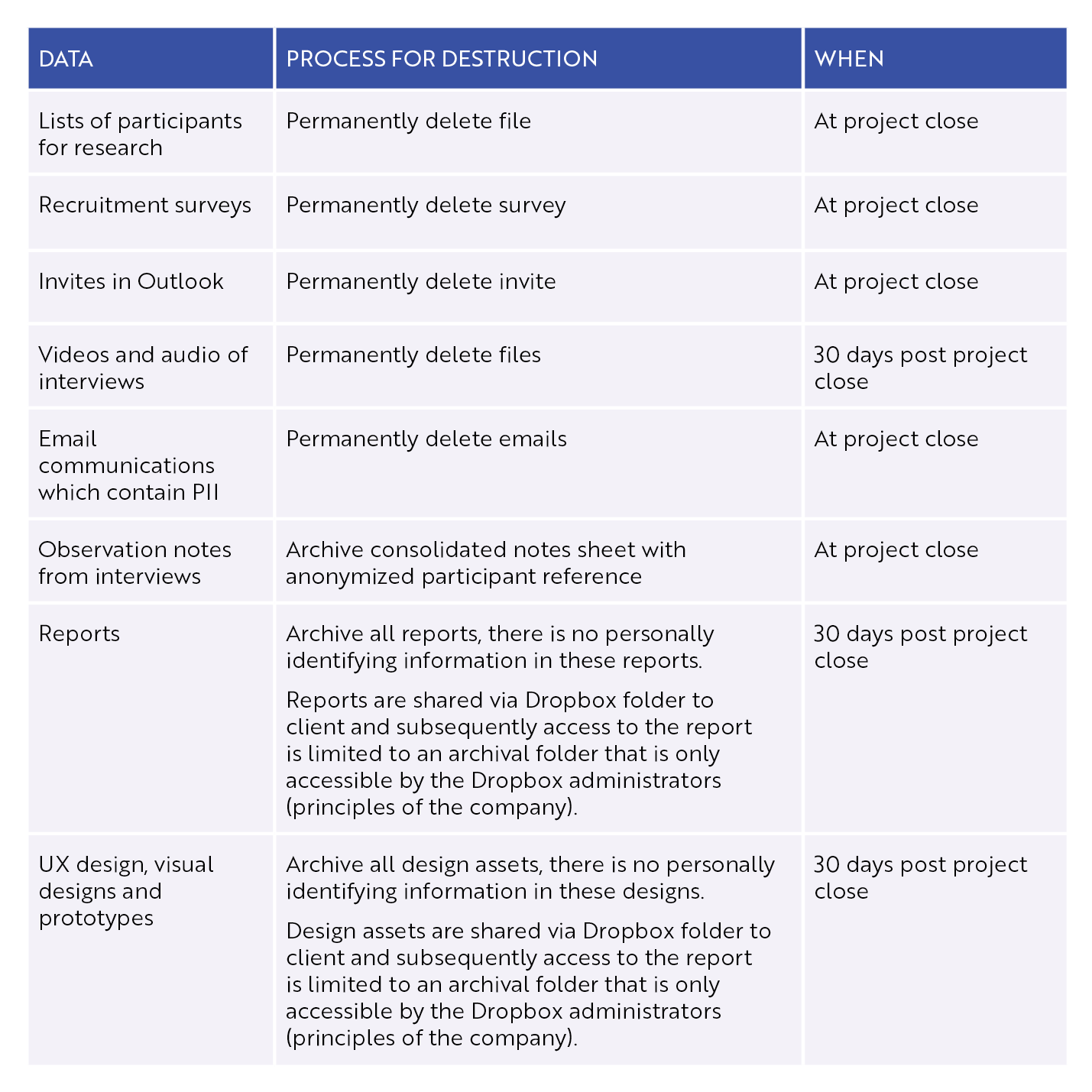
Closing the project is the most critical phase in protecting the participant and client data. It is crucial to have clear policies for what to do with data at project closure.
Permanent destruction of PII is important to reducing the risk of exposing participant data over time.
We have developed data destruction rules for the project close:
We’re a small consultancy that works with big clients, which means we need to be nimble and effective with our approach to data security.
The biggest point of failure for data security is the human element, which is why it is critical to encourage a data security mindset in your organization by implementing training, publishing guidelines, and discussing the data protection approach at the outset of every project to ensure your team knows how to handle and protect the private data that is gathered during research.
It’s also crucial to ramp up your organization’s security posture. Which I will cover in the next blog post in this series.
I presented these findings in a webinar on Tuesday, October 20, 2020. You can view that below.



